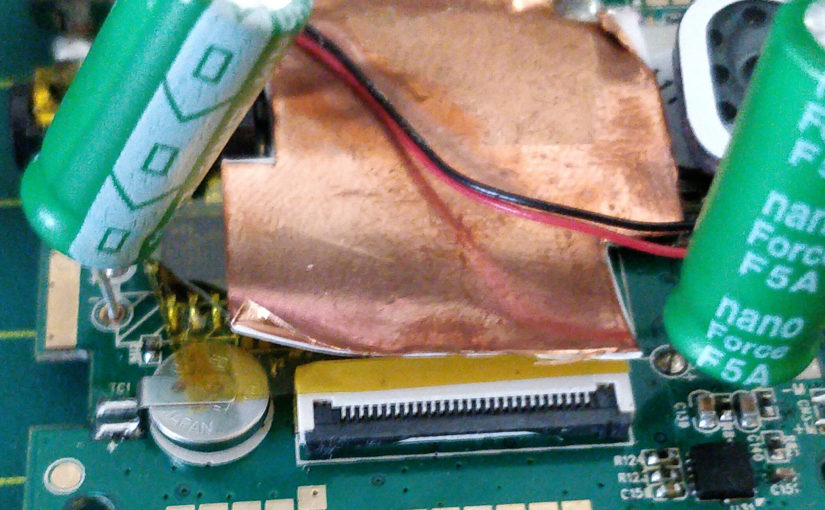
One of my A119 Cameras started to beep while presenting the “Format Yes/Cancel” prompt after long downtime. The date was also reset.
Before pandemic this was not as annoying as it would almost never do it, but with pandemic and work from home it does it pretty much every start up.
The Problem would go away once the date would be updated via GPS and the issue not come back until next very long shut down.
Continue reading Viofo A119 – Beeping with the Format prompt after a long downtime